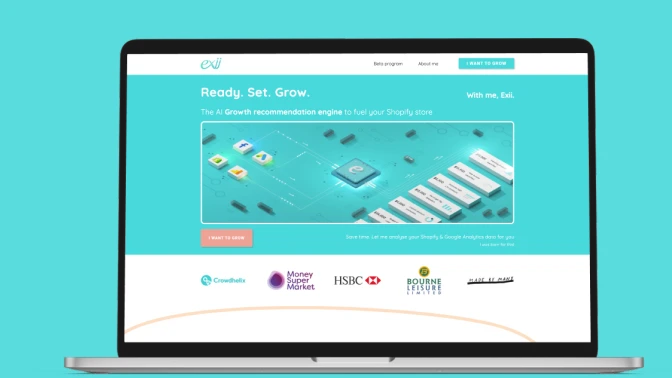
Smart Campaign Automation for E-Commerce
Exii.co recommendation engine personalizes online shopping experiences, enhancing customer engagement and increasing sales.
View MoreOperational Excellence
Tech Expertise
Consistent Commitment
Based on 43 Reviews
Proactive monitoring across multi-cloud environments
Real-time alerts with rapid incident response
Performance optimization for uptime and reliability
Continuous resource utilization and cost analysis
Auto-scaling configuration for workload stability
Infrastructure tuning for peak system performance
Ongoing vulnerability assessments and patch management
Identity access control and policy enforcement
Compliance alignment with enterprise security standards
Auditing infrastructure, risks, and optimization opportunities
Implementing monitoring, security, and redundancy controls
Continuous support, updates, and performance tuning
Improving reliability, cost efficiency, and scalability
Cloud support and maintenance services designed to prevent downtime, control cloud costs, and strengthen enterprise security across industries and SaaS platforms.
Protect mission-critical systems with proactive cloud support that reduces risk, improves performance, and ensures uninterrupted business operations.
Stabilize Your Cloud Today












Exii.co recommendation engine personalizes online shopping experiences, enhancing customer engagement and increasing sales.
View More
This AI tool provides real-time, accurate renovation cost estimates for homeowners, contractors, investors, and insurance companies.
View More
It's an AI-driven reputation management platform that automates online review collection, sentiment analysis, and response strategies to help businesses enhance their digital credibility.
View MoreServices include monitoring, performance optimization, security management, incident response, patch updates, backups, and ongoing infrastructure improvements.
Yes. We manage AWS, Azure, GCP, and hybrid environments with unified monitoring and governance strategies.
We provide 24/7 monitoring with defined SLAs to ensure rapid detection, escalation, and resolution of critical infrastructure issues.
Yes. We analyze utilization patterns, eliminate resource waste, and implement cost-optimization strategies without compromising performance.
We apply strict access controls, continuous security audits, encryption protocols, and compliance frameworks aligned with enterprise standards.